For an engineering team, the primary SIEM bottleneck is rarely the search speed or the storage limit; it is the maintenance debt of the data pipeline. As we move into 2026, the evaluation of a SIEM has moved beyond “Does it have a connector for X?” to “Who maintains the parser when the vendor updates their API?”
If your team spends a significant portion of their sprint cycles troubleshooting broken regex or manually mapping cloud logs to a schema, the platform isn’t working for you, but you are working for the platform.
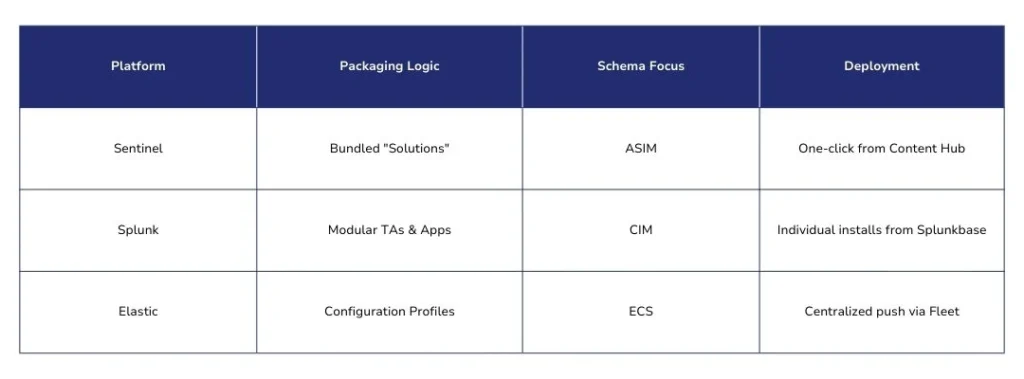
Here, we will analyze the structural differences in how Microsoft Sentinel, Splunk, and Elastic package and certify their connectors, specifically focusing on the trade-offs between “one-click” ease and granular control.
Connectors, Packaging, and Certification
To compare these platforms accurately, we need to distinguish between the pipe, the content, and the support level.
The Connector (The Pipe)
At its base, a connector is the mechanism for ingestion, whether via API polling, agent-based collection (AMA, Elastic Agent, Splunk Forwarder), or standard protocols like Syslog and CEF. In a mature SOC, a connector is only as good as its normalization logic. A raw JSON dump into an index is a data lake, not a SIEM; without mapping to a schema, your cross-source correlation queries simply won’t work.
Packaging Models (The Content)
The market has split into two distinct philosophies:
- Standalone/Modular: The connector brings in the data, but the detection rules, dashboards, and playbooks are separate entities. This is traditional and flexible but requires manual “wiring.”
- Bundled Solutions: Common in the Sentinel ecosystem, this approach treats a data source as a “Solution.” Installing it deploys the connector and simultaneously populates the workspace with relevant analytics, hunting queries, and automation workbooks.
Packaging Models (The Content)
The market has split into two distinct philosophies:
- Standalone/Modular: The connector brings in the data, but the detection rules, dashboards, and playbooks are separate entities. This is traditional and flexible but requires manual “wiring.”
- Bundled Solutions: Common in the Sentinel ecosystem, this approach treats a data source as a “Solution.” Installing it deploys the connector and simultaneously populates the workspace with relevant analytics, hunting queries, and automation workbooks.
Packaging Models (The Content)
Certification isn’t just a marketing badge; it defines the support lifecycle.
- Vendor-Backed: The SIEM vendor owns the code. If the API breaks, they fix it.
- Partner-Verified: A third-party vendor (e.g., CrowdStrike or Cisco) maintains the integration to ensure it works with their product updates.
- Community/Open-Source: High-velocity but high-risk. These are often the first to market for new vulnerabilities, but may be abandoned if the original author moves on.
How Each Platform Handles Connectors & Packaging
The architectural philosophy of your SIEM dictates whether you spend your time on security outcomes or data engineering. While all three platforms offer connectivity to major sources, their packaging and delivery models are fundamentally different.
Microsoft Sentinel: The “Solution-Centric” Content Hub
Microsoft has moved away from treating connectors as isolated components. Instead, they utilize a Solution-centric model housed in the Content Hub.
- The Bundle: When you deploy a solution (e.g., for CrowdStrike or Cisco ASA), you aren’t just installing a pipe. The solution bundles the Data Connector, Analytics Rules (detections), Hunting Queries, and Workbooks (dashboards) into a single deployment.
- The 2026 Shift (CCF): Microsoft is currently deprecating legacy Azure Function-based connectors in favor of the Codeless Connector Framework (CCF). This is a SaaS-managed experience that removes the need for customers to manage the underlying compute or credential storage for API polling.
- Support Tiers: Sentinel provides a very clear governance hierarchy: Microsoft-supported, Partner-supported, and Community-supported. For mission-critical ingestion, this transparency is vital for risk management.
Splunk: The Modular Marketplace (Splunkbase)
Splunk’s ecosystem is the most mature, but it follows a modular, “Build-A-Bear” philosophy.
- Technology Add-ons (TAs): In Splunk, the connector is typically a TA. Its primary job is to ingest the data and map it to the Common Information Model (CIM).
- Separation of Concerns: Unlike Sentinel, the detection logic (the “App”) is often a separate installation. For example, you might install the Splunk Add-on for AWS for ingestion and the Splunk App for AWS for visibility.
- Certification: Splunkbase uses “Splunk Reinforced” or “Splunk Certified” badges. While Splunk has 1,500+ integrations, a high percentage are community-authored. This requires practitioners to perform more rigorous QA before deploying a community TA into a production search head cluster.
Elastic: The Integration Factory (Fleet)
Elastic takes an “Integration-first” approach, focusing heavily on performance at the edge via Elastic Agent and Fleet.
- Elastic Integrations: These are configuration-driven profiles. Rather than installing “software,” you enable an integration that defines an Ingest Pipeline. This pipeline parses and enriches data, mapping it to the Elastic Common Schema (ECS) before it ever hits the disk.
- Global Fleet Management: As of early 2026, Elastic’s Global Fleet allows for multi-cluster synchronization. You can define an integration once and push it across global clusters, ensuring your parsers and policies stay consistent across data centers.
- Agent Builder: A significant 2026 addition is the Agent Builder, which allows engineers to use AI-assisted workflows to generate custom integrations for bespoke internal applications that lack an official connector.
Certification & Governance Comparison
When a log source changes its format, your detection coverage drops. In a decision-making context, certification isn’t a trophy; it’s an insurance policy. The difference between these platforms lies in who bears the risk of that insurance.
The Support Tier Reality
In 2026, the governance models have matured to address the “Community abandonment” issue, but the transparency of this risk varies by platform.
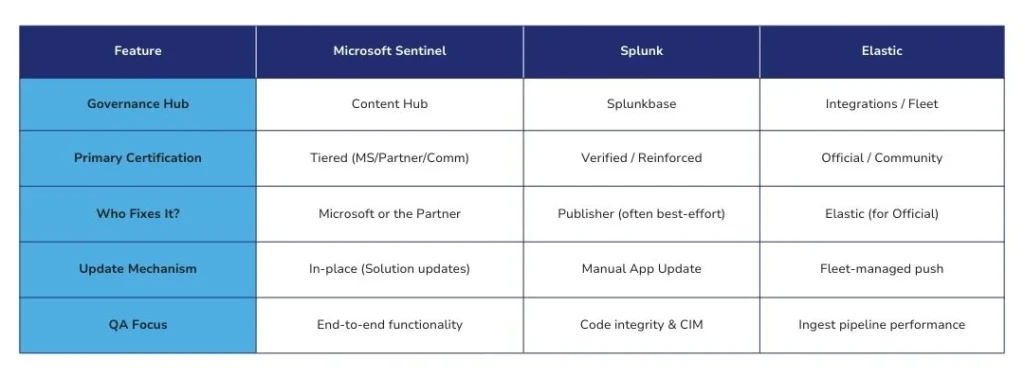
Key Insights for Decision Makers
Sentinel: The “SaaS-Managed” Safety Net
Sentinel’s Microsoft-supported tier is the most rigid. If a Microsoft 365 or Azure API changes, Microsoft updates the connector automatically. For partner-supported solutions (e.g., Palo Alto or Fortinet), the certification requires the partner to maintain the code to stay in the Content Hub. This reduces the “Day 2” operational burden significantly.
Splunk: The Width vs. Depth Dilemma
Splunkbase is the industry’s largest library, but that breadth is a double-edged sword. A “Verified” app on Splunkbase means the code passed Splunk’s security and performance scans, but it does not always guarantee that the author will update it for a new API version. For enterprise-grade reliability, you must verify if the TA is built by Splunk’s Global Strategic Alliances or an individual developer.
Elastic: The “Integrated” Advantage
Elastic doesn’t treat integrations as third-party plugins. “Official” integrations are part of the Elastic Stack itself. This means they are tested against every minor and major release of the platform. If you are using an official Elastic Integration for AWS, it is virtually guaranteed to work on version 9.2 just as it did on 8.15.
Connector Quality Signals: Evaluation Criteria
If you are vetting a new integration for a production environment, looking at the “connector count” is a vanity metric. Instead, look for these three signals of Functional Completeness:
- Schema Consistency (ASIM, CIM, ECS): Does the connector map to a standard schema out of the box? If it uses custom field names (e.g., src_ip vs SourceIp), your hunting queries will break when you pivot between sources.
- Enrichment at the Edge: Does the connector perform Geo-IP, Threat Intel lookups, or user-agent parsing at ingestion? Doing this post-ingestion (at search time) is an “expensive” query-side tax.
- Deprecation Transparency: How does the vendor handle legacy integrations? Microsoft’s 2026 move to the Codeless Connector Framework (CCF) is a prime example of a platform forcing a move toward more stable, managed connectivity.
Common Pitfalls & High-Scale Realities
Even with “Certified” connectors, enterprise deployments often hit three specific walls:
The “Lazy JSON” Trap: Some connectors ingest logs as a single, unparsed JSON blob. While this makes ingestion “fast,” it makes search “slow” and expensive. Always verify that your connector performs field extraction at ingest time.
Schema Drift: A vendor updates their API, adding a new field or changing a timestamp format. If your connector isn’t Vendor-Supported, you are responsible for updating the regex. In 2026, look for platforms moving toward OCSF (Open Cybersecurity Schema Framework) to mitigate this risk.
The “Hidden” Compute Cost: For cloud-native SIEMs, some connectors require an intermediate “Function” (like an Azure Function or AWS Lambda) to poll an API. The cost of that compute often isn’t included in the SIEM licensing and can spike during high-traffic events.
Choosing Your Trade-off
There is no “best” model, only the one that fits your team’s DNA.
- Choose Microsoft Sentinel if you want to minimize engineering overhead and maximize out-of-the-box detection value.
- Choose Splunk if you have a diverse, complex environment that requires the industry’s broadest set of modular integrations.
Choose Elastic if you prioritize ingestion performance and want a unified “Observability + Security” pipeline.
Closing the Visibility Gap
Selecting a SIEM is only half the battle; the other half is ensuring that your critical data sources don’t fall through the cracks of “community-supported” or generic connectors. If you find that your current ecosystem lacks a high-fidelity, schema-compliant connector for a bespoke or emerging tool, you don’t have to bear the engineering tax alone.
At ForshTec, we specialize in developing enterprise-grade, certified-ready connectors for Splunk, Sentinel, and Elastic. We ensure your data isn’t just “ingested,” but fully normalized and detection-ready from day one.
Contact us today to discuss how we can help you eliminate your connector maintenance debt and accelerate your SOC’s time-to-visibility.

